Email Security
Block any email-borne threat, including spam, phishing, business email compromise (BEC), malware, advanced persistent threats (APTs), and zero-days before it reaches end-users.

Overview:
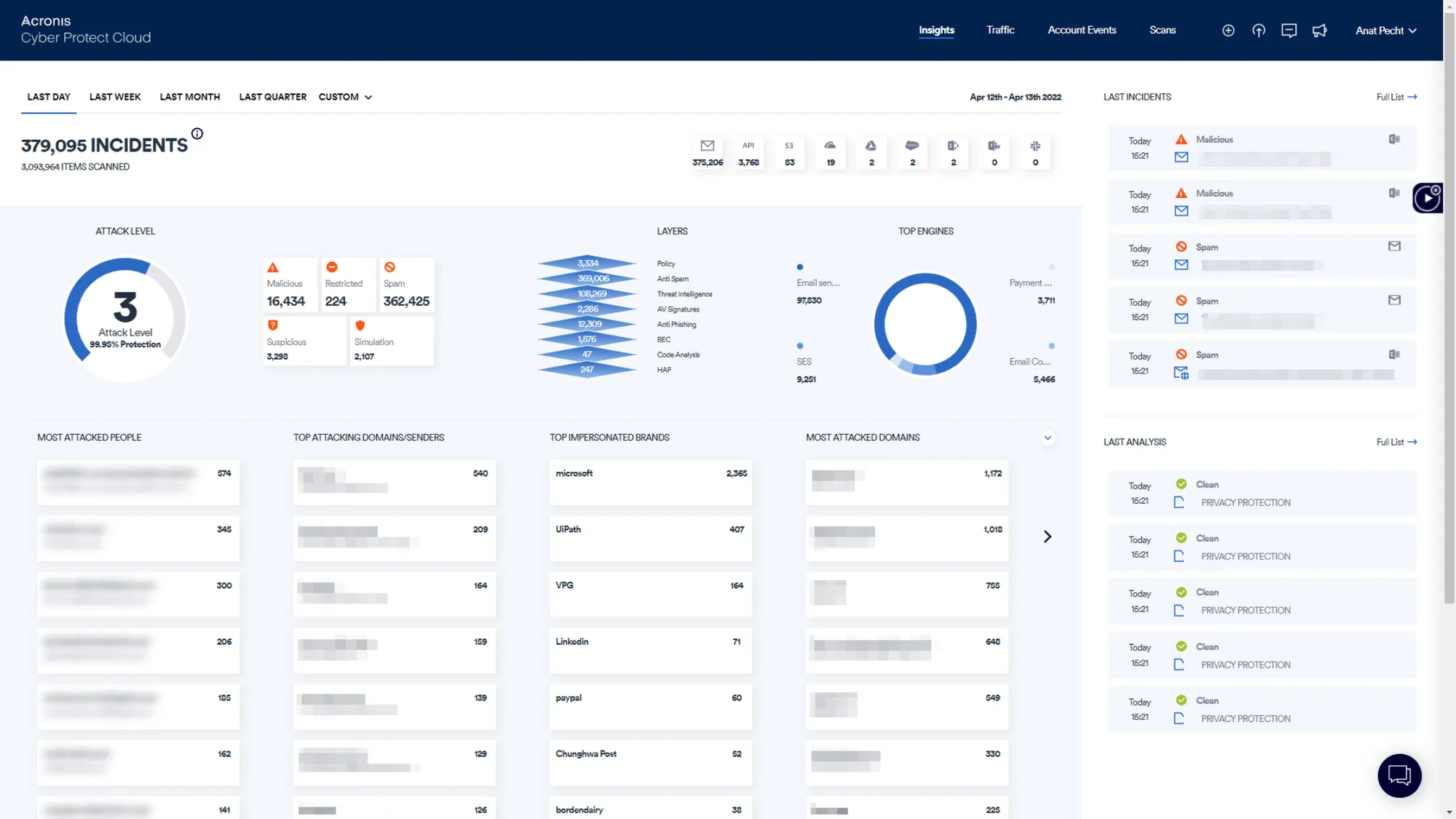
Intercept modern email-borne attacks within seconds
Block email threats, including spam, phishing, business email compromise (BEC), account takeover (ATO), malware, advanced persistent threats (APTs), and zero-days before they reach end users’ mailboxes. Leverage this next-generation, cloud-based email security solution for holistic protection.
Stop phishing and spoofing attempts
Minimize email risk for clients with powerful threat intelligence, signature-based detection, URL reputation checks, unique image-recognition algorithms, and machine learning with DMARC record checks.
Catch advanced evasion techniques
Detect hidden malicious content by recursively unpacking embedded files and URLs and separately analyzing them with dynamic and static detection engines.
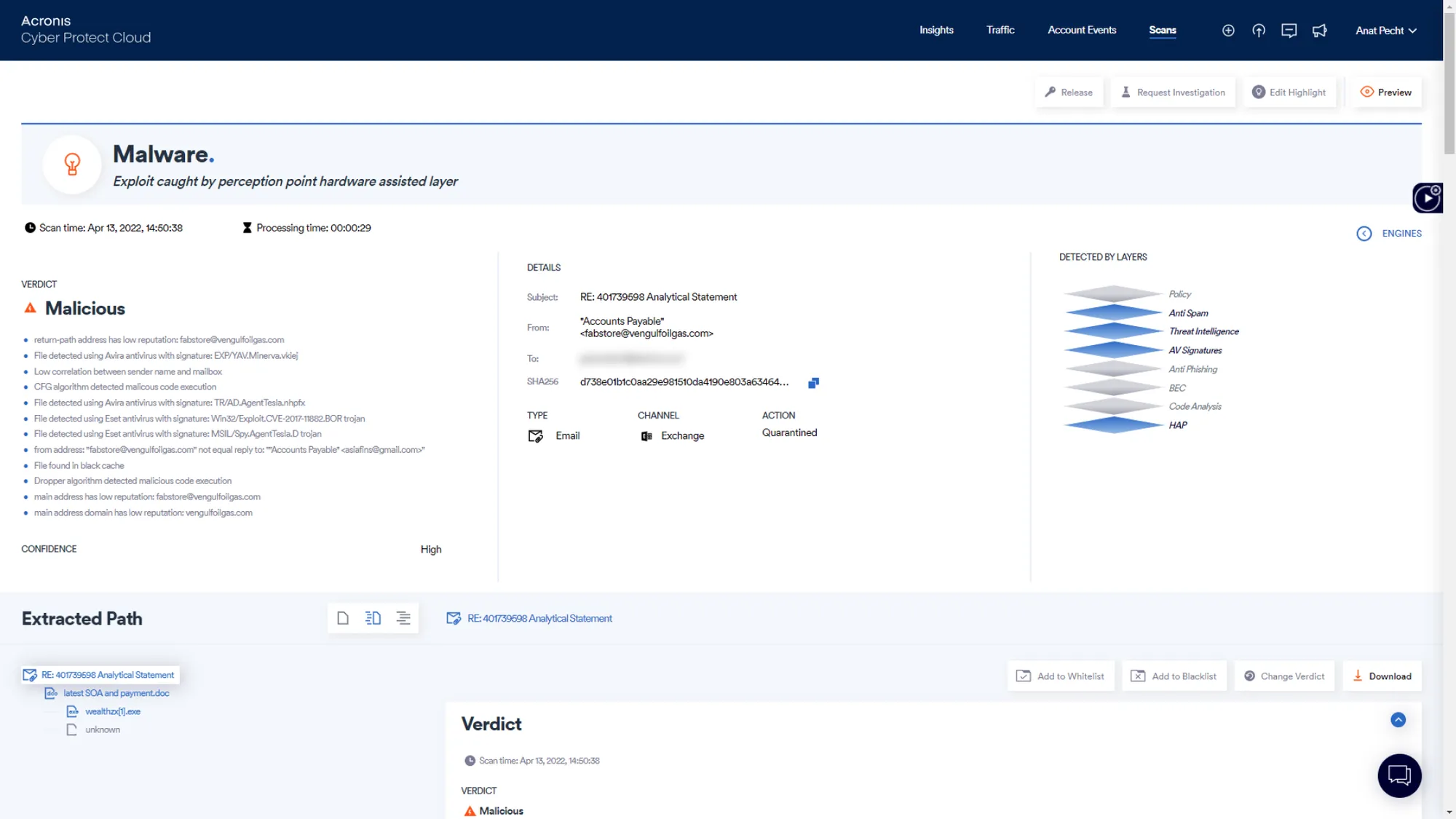
Prevent APTs and zero-day attacks
Prevent advanced email threats that evade conventional defenses with a unique CPU-level technology able to act earlier in the attack chain to block exploits before malware is released, delivering a clear verdict within seconds.
Collaboration App Security for Microsoft 365
Better security for your clients’ critical cloud collaboration applications.
Enhance your cyber protection services with cloud email security
Email is the biggest threat vector for your clients - neutralize it and minimize risks in email communication with a unique technology. Email Security enables you to offer more thorough cyber protection without increasing your management burden.
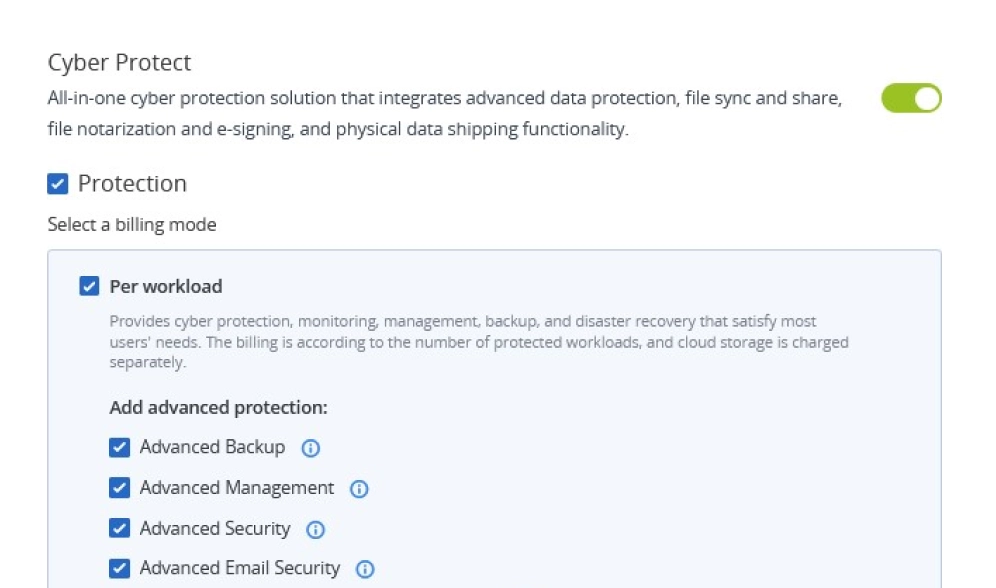
Rapidly turn up and provision services
Expand or enhance your services with proven cloud-based email security to meet clients’ rapidly growing security requirements with confidence. Start planning the upgrade of your services without worrying about the time needed to implement; email security is enabled with the flip of a switch and via API-based provisioning for Microsoft 365. Leverage consumption-based pricing and upgrade your costs, margins, profitability, and business plan to secure better additional streams.
Protect your clients’ #1 threat vector from any type of email attack
Phishing emails account for more than 90% of attacks. Minimize the risks for clients when communicating via email and stop threats before they reach their Microsoft 365, Google Workspace, Open-Xchange, or other cloud-based or on-premises mailboxes. Intercept modern email threats, including spam, phishing, business email compromise (BEC), account takeover (ATO), spoofing, malware, zero-days, and advanced persistent threats (APTs) in mere seconds with zero false positives. Enhance compliance and increase visibility into admin users and incident response team actions with a comprehensive audit log. Build your services on top of a leading email security solution that scans 100% of traffic at any scale.
Consolidate and streamline your services while saving time and resources
Modernize your security stack with a single solution that ingrates cloud-based email security with backup, recovery, endpoint protection, DLP, and cyber protection management. Reduce the resources needed to deliver multiple services and cut costs through solution consolidation. Significantly reduce the deployment complexity associated with secure email gateways (SEGs) and leverage a cloud-native deployment - up to a few minutes without the need for additional mail exchanger record (MX record) configurations. Increase risk visibility across all email security alerts and incidents.
Build your services on a leading email security solution in SELabs evaluations
Replace the inefficient security stack of sandboxes and content disarm and reconstruction technologies (CDRs) with a multi-layered email security solution for lightning-fast detection that’s easy to deploy and manage.
![]()
Scan 100% of traffic in real-time
Scan content across inbound and outbound emails, and prevent lateral movement. Unlike legacy sandboxing solutions, every bit of content - emails, files, and URLs - is analyzed at any scale.
![]()
Prevent APTs and zero-days
Block sophisticated threats that evade conventional defenses such as APTs and zero-day attacks with a unique CPU-level analysis that allows action earlier in the attack chain than other technologies.
![]()
Effortless, rapid deployment
Cloud-native deployment that integrates directly with the email system without additional configurations, including API-based for Microsoft 365. Reduce the administrative burden associated with a standard secure email gateway (SEG) deployment.
![]()
Incident response services
Empower your service delivery and security teams with direct access to cyber analysts and email security experts that monitor all customer traffic and analyze malicious intents with ongoing reporting and support.
![]()
Unmatched detection speed
Leverage an unmatched detection speed that allows you to prevent all threats before they reach end-users, compared to the reactive approach of standard email security technologies.
Stop email-borne threats before they reach end-users

Malware and ransomware
Malware – including viruses, ransomware, spyware, worms, and Trojans - is most commonly delivered via malicious payloads – files and URLs. Thousands of new malware variants appear each day. Legacy solutions fall short when dealing with advanced evasion techniques and defending collaboration platforms.
Email Security helps you stop malware with multi-layered defenses, including:
- Anti-evasion – Detect hidden malicious content
- Threat intelligence – Stay ahead of emerging threats
- Anti-phishing filters – Detect malicious URLs
- Antivirus engines – Stop known malware
- Next-generation dynamic engine – Catch zero-days and APTs that evade conventional defenses

Phishing
Phishing attacks are the root of 91% of all cyberattacks, as reported by CSO Online. They leverage social engineering to deceive their target and gain access to sensitive information by employing files, URLs, and text-based techniques posing as legitimate sources.
Email Security helps prevent phishing before it reaches end-users with:
- Anti-evasion – Unpack deeply embedded, hidden phishing attempts
- URL reputation – Block known, malicious URLs based on four leading URL reputation engines
- Image recognition engine – Block unknown malicious URLs based on the images and logos used on webpages
- Threat intelligence – Combine six market-leading sources and Perception Point’s unique engine

Business email compromise (BEC)
Impersonation-based attacks trick employees into making innocent mistakes, thinking they’re communicating with a person they know. A significant part of BEC attempts do not have a malicious payload and leverage only text-based techniques, making them especially tricky to detect and prevent.
The Email Security helps prevent impersonation attempts with:
- Anti-spoofing - Prevent payload-less attacks through machine-learning algorithms with IP reputation, SPF, DKIM, and DMARC record checks
- Anti-evasion – Deep scan to detect malicious hidden content
- Payload-based protection – Reduce “further along the line” BEC attacks with threat intelligence, phishing, and antivirus engines

Zero-days and APTs
Zero-days and APTs are especially hard to catch and prevent. They can lie in wait and strike months before they’re discovered by leveraging unknown software vulnerabilities. Standard APT modules, such as sandboxes or content disarm and reconstruction solutions (CDRs), rely on known data and behaviors that evasion techniques can mask when in a sandbox.
Email Security's market-leading technology helps you prevent zero-days and APTs:
- Next-generation dynamic scan – Stop zero-days and APTs with a unique CPU-level technology that detects and blocks advanced attacks at the exploit stage, before malware release, based on the assembly code
Evasion techniques
Email-borne attacks are getting trickier to detect. Attackers use evasion techniques such as new file types, link chains, malicious content hidden within clean files, stalling mechanisms that sandboxes can’t observe, ensuring the malicious payload takes action only when facing actual end-users. For conventional defenses, preventing such techniques is almost impossible as it takes too much time, money, and technological resources.
The Email Security uses unique technology to prevent evasion techniques that conventional defenses miss:
- Anti-evasion - Recursively unpack the content into smaller units which are then dynamically checked by multiple engines in under 30 seconds, compared to 20+ minutes for legacy sandboxing solutions.

Account takeover (ATO)
Account takeover (ATO) has been increasingly commoditized through the cybercriminal ecosystem — whether the target is business email or a company’s bank accounts. Known also as account compromise, ATO occurs when a cyber attacker gains control of a legitimate account. Once they have control of an account, attackers can launch a variety of attacks, such as supply-chain phishing, BEC attacks, data exfiltration, financial fraud, etc. There are no preliminary signs of such an attack; in most cases, once the signs of ATO are obvious, the damage has already been done.
Email Security helps you to intercept account takeover attempts, at any stage — ready to prevent, detect, and rapidly respond with multiple defense layers.
- Prevent credential theft — block phishing attempts to steal employees’ credentials with multiple engines
- Monitor accounts for signs of compromise — analyzes end user patterns and behaviors and uses machine learning algorithms to detect anomalies that could suggest an account has been compromised
- Instantly detect and remediate compromised accounts — ensure fast remediation and account containment by the incident response team in the event of account takeover
Protect not just emails, but clients’ riskiest collaboration tools
Protect clients’ collaboration apps, increasingly exploited in attacks with prioritized patching and exploit prevention. Leverage Acronis Cyber Protect Cloud, integrating backup and disaster recovery, next-generation anti-malware, and cyber protection management.

Protect clients’ riskiest communication channel with unmatched detection technologies
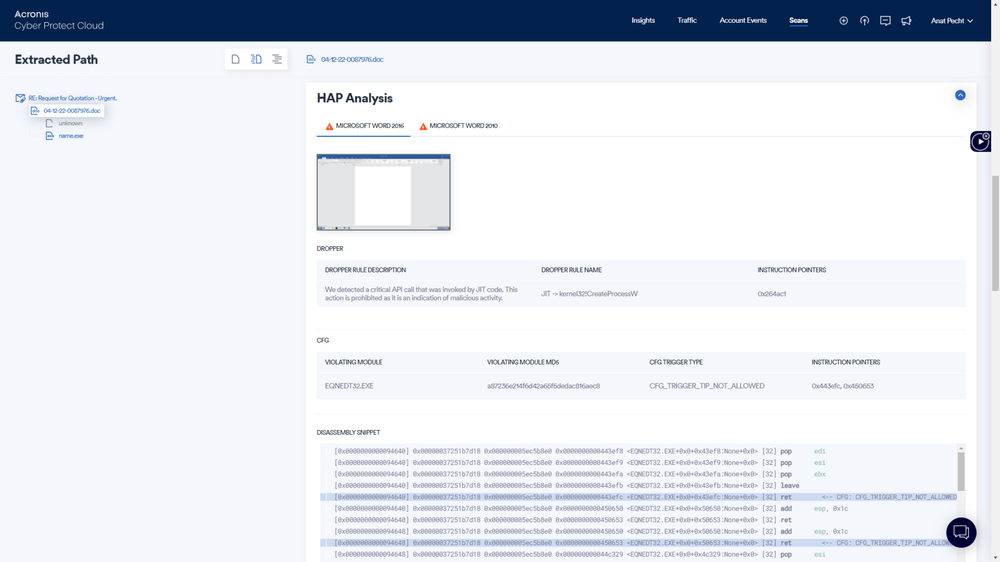
Next-generation dynamic scan
Stop zero-days and APTs with a unique CPU-level technology that detects and blocks advanced attacks that evade conventional defenses at the exploit stage by identifying deviations from normal execution flow during runtime.
![]()
Microsoft 365 outbound email scanning
Reduce reputational risks for clients by detecting malicious emails originating from their mailboxes via Microsoft 365 API-based scanning. Also enhances inbound protection accuracy through analysis of communications with external parties.
![]()
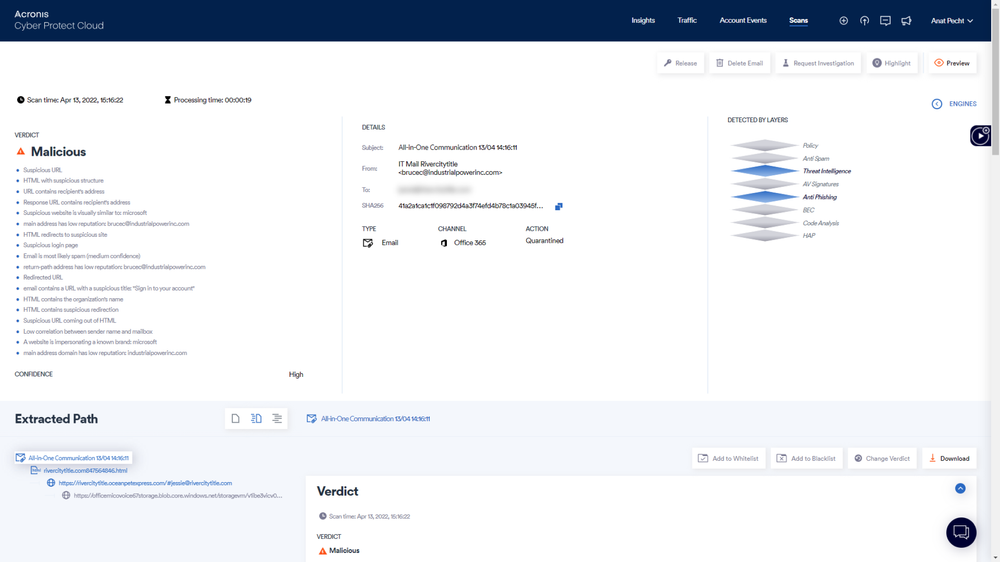
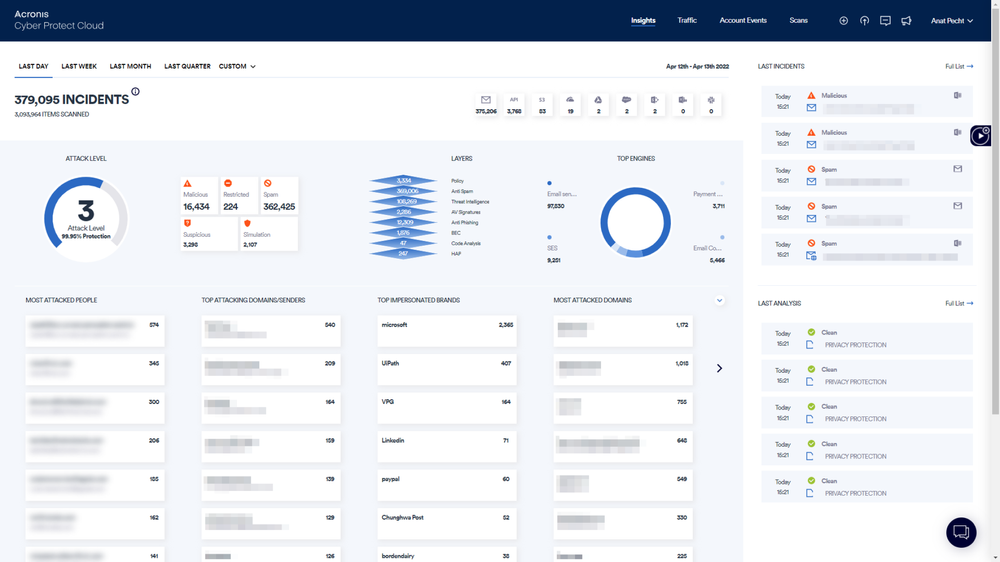
X-ray insights
Leverage a holistic view of the threat landscape across organizations with forensics data for each client and email, proactive insights on threats a targeting clients and most risky attack patterns, and analysis of any file or URL on which your team needs forensics.
![]()
Incident response service
Gain direct access to cyber analysts that act as an extension of your service delivery team, monitor all customer traffic, and analyzing malicious intents with ongoing reporting and 24/7 support, including handling false positives, remediating, and releasing as required.